SearchStax Site Search Single Sign-On (SSO) Setup for Okta
The SearchStax Site Search solution now offers the ability for customers to set up Single Sign-On (SSO) to let their users log into SearchStax apps with a single ID and password that works across multiple software systems.
We use the open standard Security Assertion Markup Language (SAML) to allow identity providers (IdP) to pass authorization credentials to service providers (SP). This page provides instruction to use Okta to implement SSO for SearchStax.
SSO is an add-on SearchStax feature that is purchased separately as part of the Security Pack. If you are interested in the Security Pack, please contact Sales.
Once SSO is enabled for your account and a domain is set up, the admin is able to see the configuration options in the User Preferences screen of the Site Search Dashboard.
The following steps explain how it can be set up for Okta.
Instructions
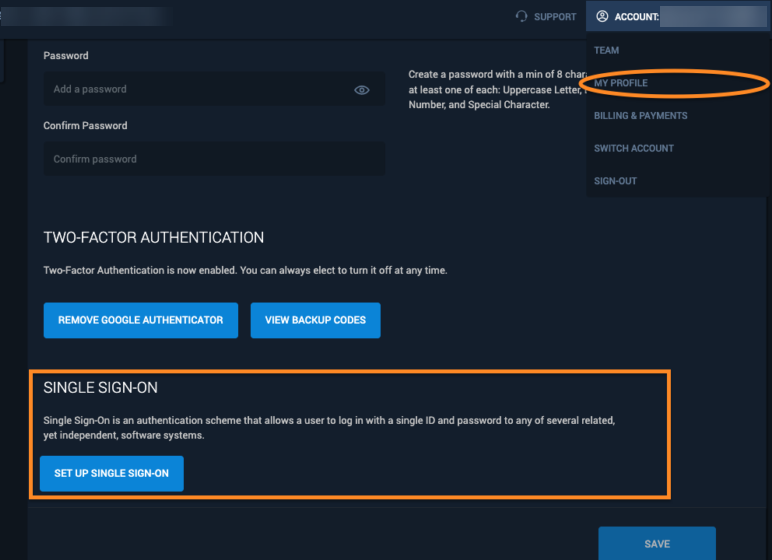
Once SSO is enabled by SearchStax for your account, and a domain is set up, the owner and/or admin can see options to set it up. The options to set up SSO are in the My Profile screen of the SearchStax Site Search Dashboard:
1. You need to be an Admin in Okta to set up the SearchStax Application.
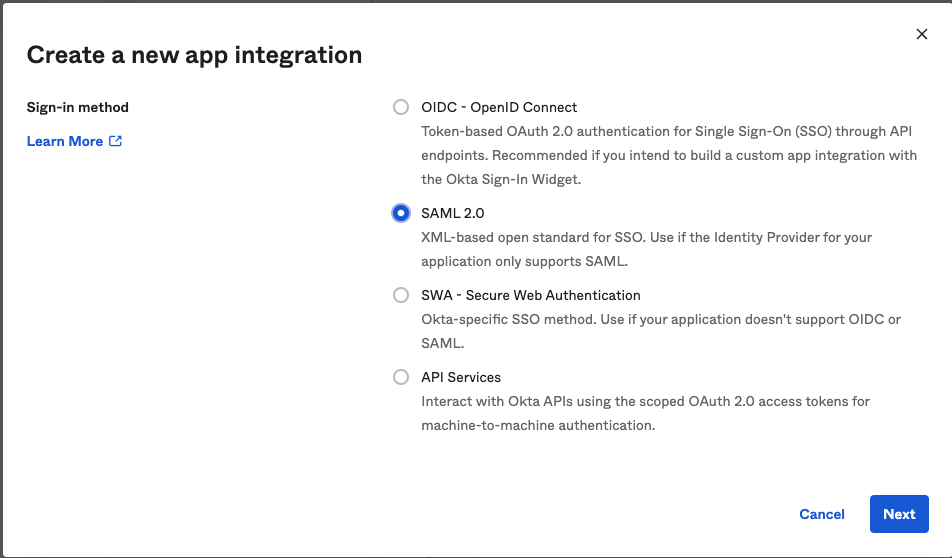
2. Go to the Okta Admin Console. Click on Applications > “Create App Integration”. Select “SAML 2.0” and click on “Next”
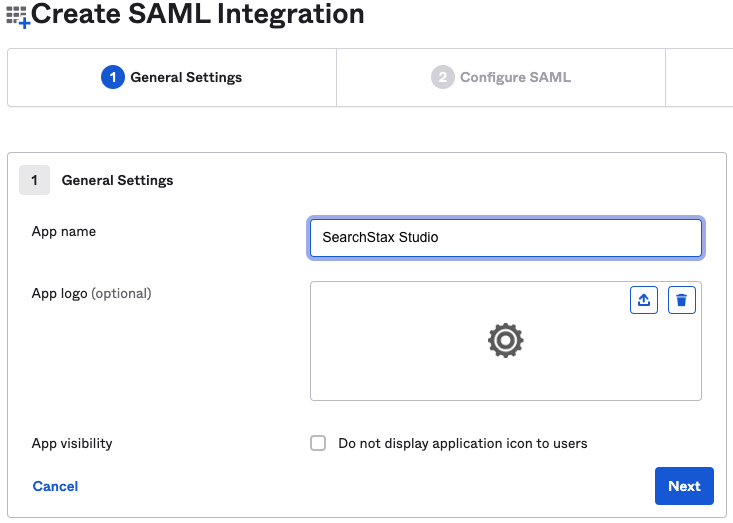
3. Enter the name of the App as “SearchStax Studio” and click on Next
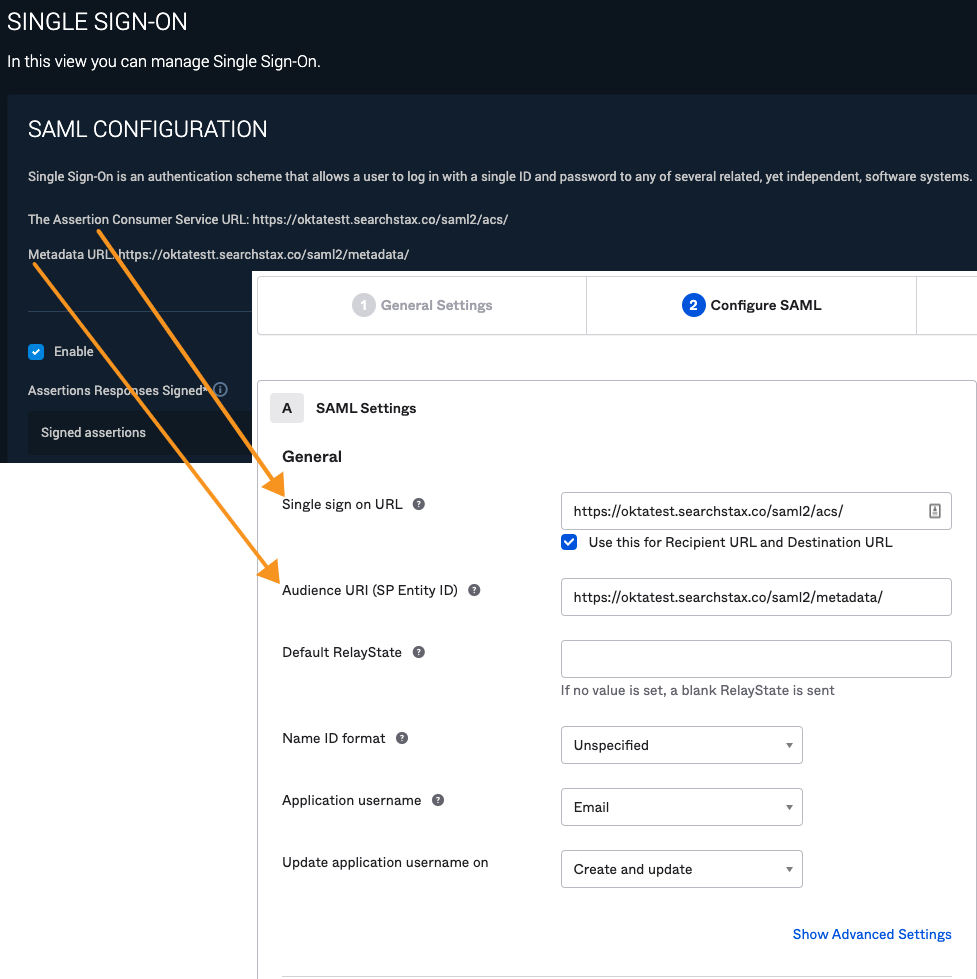
4. Configure the SAML Settings with the following information:
- Set the “Single sign on URL” as the The Assertion Consumer Service URL provided in Site Search
- Check on “Use this for Recipient URL and Destination URL”
- Set the “Audience URI”as the Metadata URL provided in Site Search
- Set the “Name ID format” as “Unspecified”
- Set the “Application username” as “Email”
- Set the “Update application username on” as “Create and update”
5. Click on “Show Advanced Settings” and set “Response” and “Assertion Signature” to “Signed”. Below is a sample of Advanced Settings
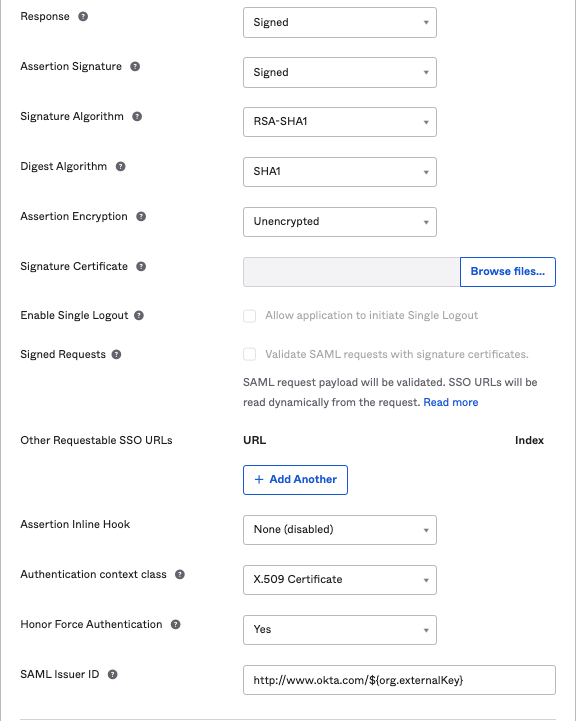
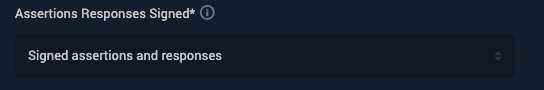
*If you change the response and assertion settings, you will need to also change the Site Search “Assertions responses signed*” setting to match.
6. The next section provides Attribute Statements for mapping Okta fields to SearchStax. Below are sample mappings that we defined
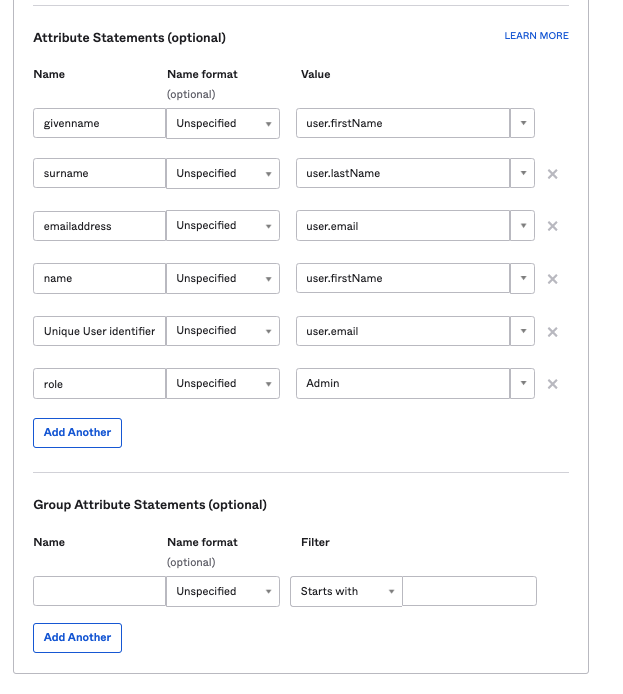
The above example assigns the role of “Admin” to all users in Site Search. However, if you have a different field in Okta that maps the role, you can assign that field instead.
Click on Next.
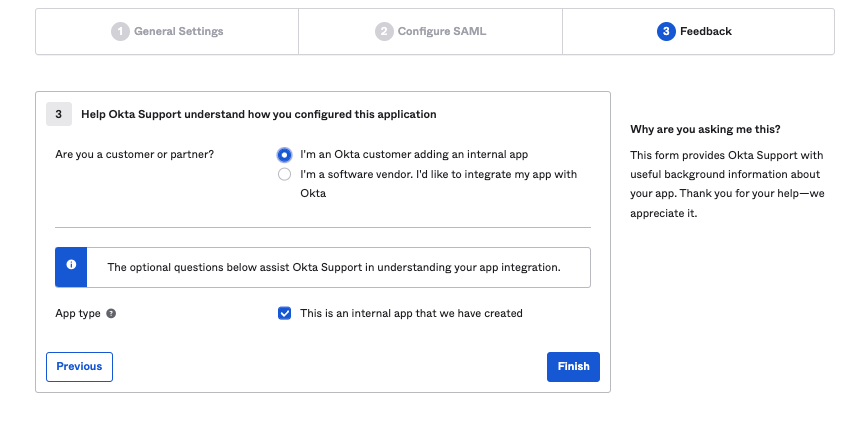
7. Select “I’m an Okta customer adding an internal app” and click on “Finish”
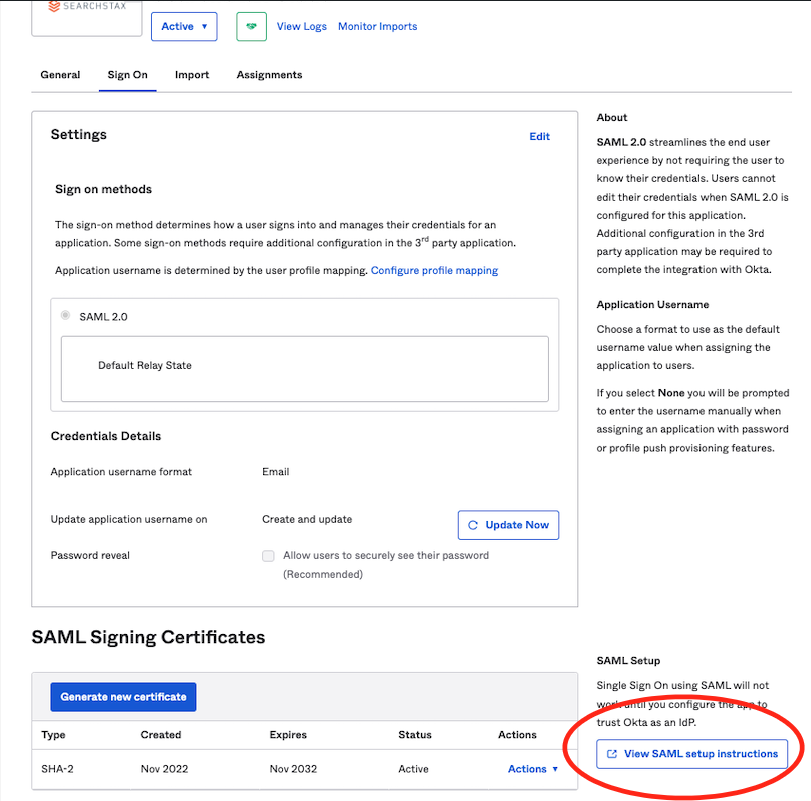
8. Now click on the “View SAML setup instructions” button that is displayed to the right
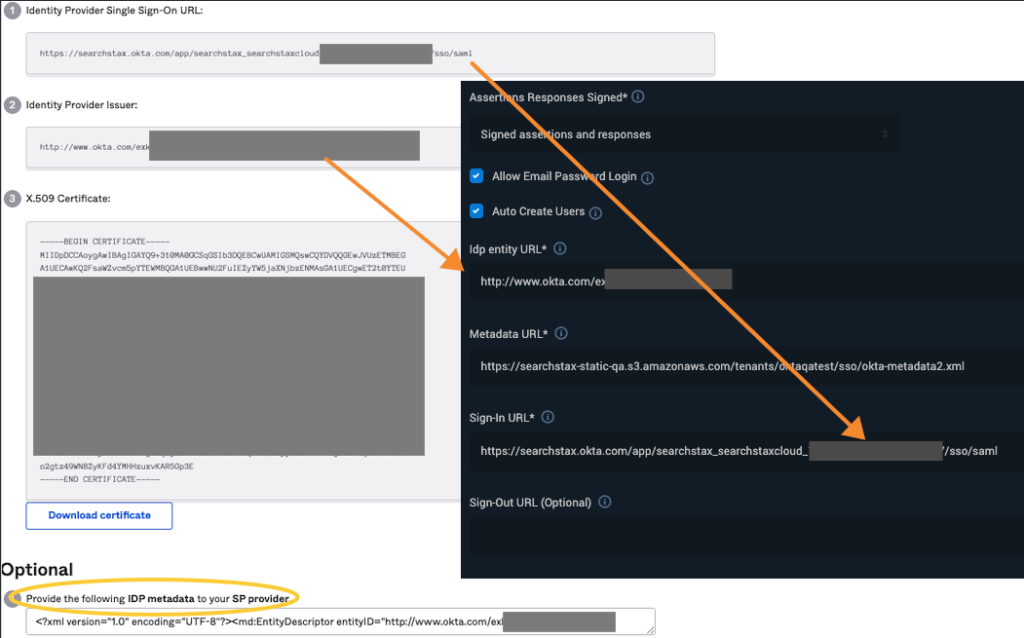
9. Copy the “Identity Provider Single Sign-On URL” from the screen and set it as the Login url in Site Search.
10. Copy the “Identity Provider Issuer” from the screen and set it as the Idp entity url in Site Search.
11. Copy the XML shown in the Optional section with the title “Provide the following IDP metadata to your SP Provider” and host it on a URL (optionally, you can send it to us and we can host this for you). Copy this hosted IDP metadata URL and set it as the Metadata url in Site Search.
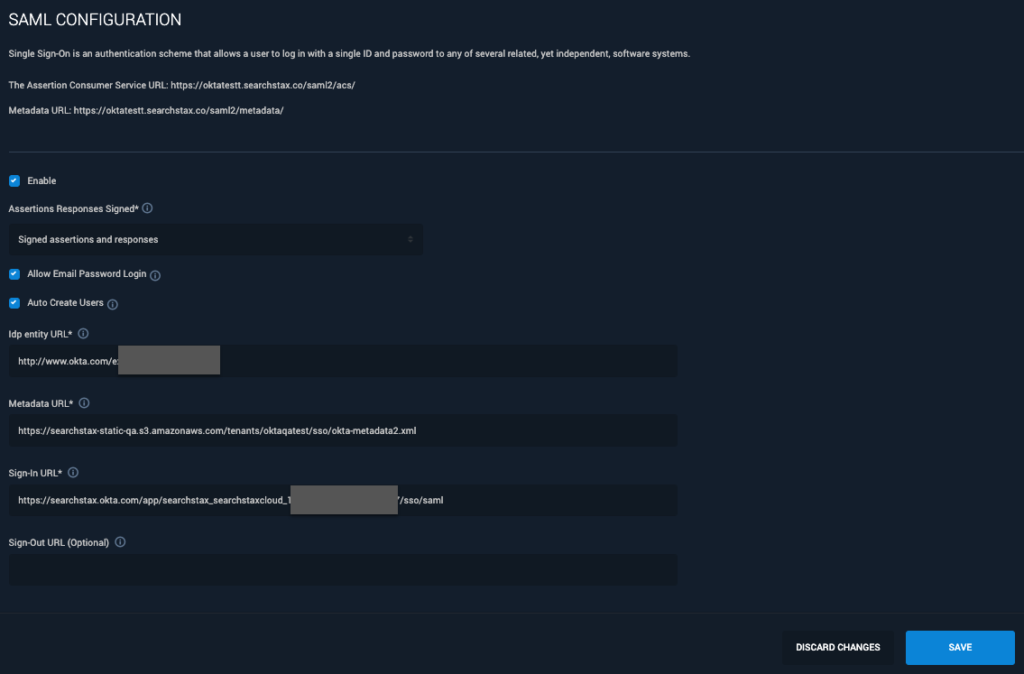
12. Now, set SSO to “Enabled”.
When you are testing, also check “Allow email password login” (You can turn this off once SSO testing is complete). Here is our example setting page:
Login Using SSO
On https://searchstudio.searchstax.com/ , click the “Sign-In using your ID provider” button.
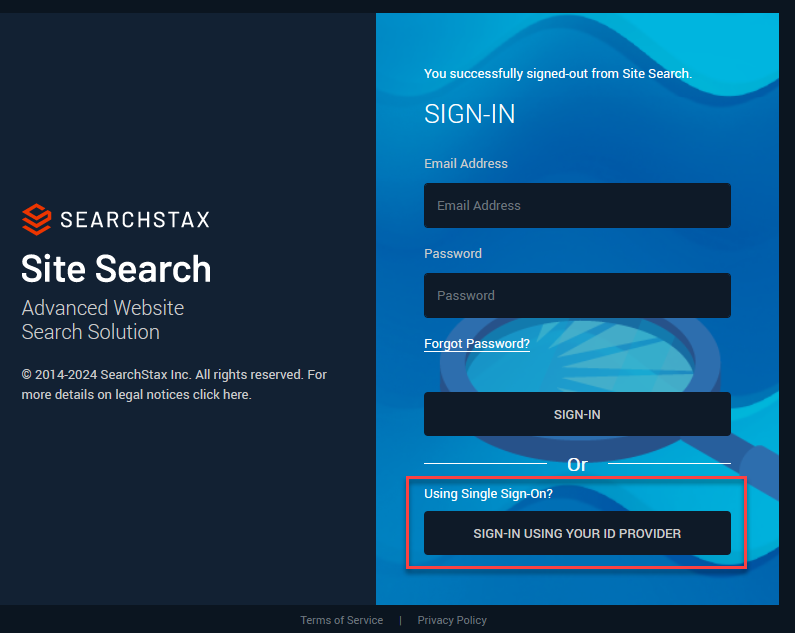
Enter the domain.
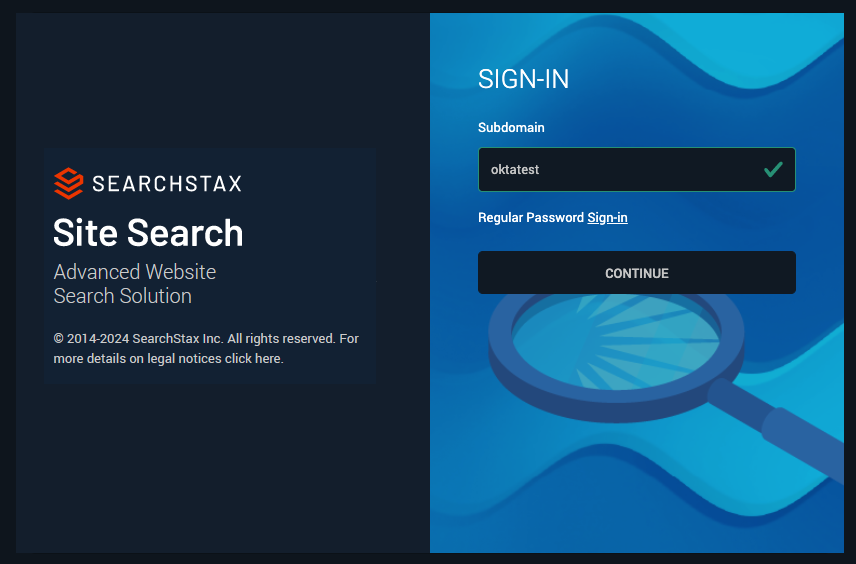
Click Continue. This takes you to the Okta Sign-in page. After you authenticate, it brings you back to your SearchStax Site Search Dashboard.
SSO + Two-factor Authentication
A User can have SSO and Two-Factor authentication both setup. The 2FA settings for a user will apply to all accounts that the user has access to.
However, for the account that has SSO Setup, while logging in, SearchStax 2FA settings will not apply. In that case, 2FA should be set up at the SSO Provider.
Questions?
Do not hesitate to contact the SearchStax Support Desk.

