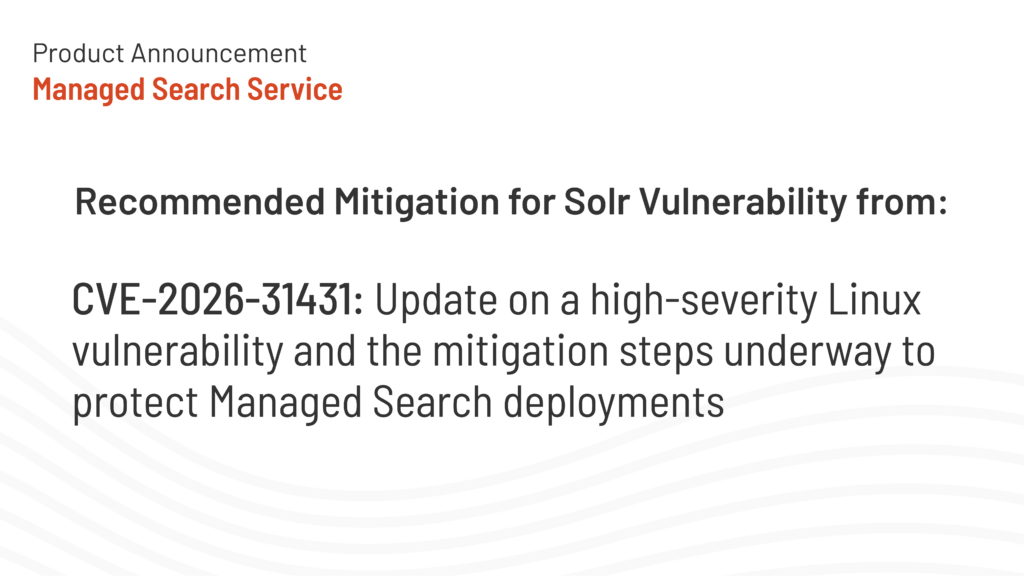
SearchStax is tracking a Linux kernel vulnerability identified as CVE-2026-31431. The vulnerability has been assigned a CVSS score of 7.8, which is classified as High severity.
This post summarizes what is currently known, which deployments may be affected, what SearchStax is doing and whether customers need to take any action.
Summary
CVE: CVE-2026-31431
Severity: High
CVSS Score: 7.8
Vulnerability Type: Local privilege escalation
Affected Systems: Linux deployments running kernel versions released after 2017
Customer Action Required: None
Expected Service Downtime: None expected
Vulnerability Details
CVE-2026-31431 affects part of the Linux kernel’s cryptographic interface.
The issue involves an incorrect in-place operation where the source and destination data mappings differ. Under certain conditions, this may cause data integrity issues. Because the vulnerability is classified as a local privilege escalation, successful exploitation could allow a local user or process to gain elevated privileges, including root-level access.
This type of vulnerability is most relevant when an attacker already has some level of access to an affected Linux system. The risk is that the attacker may be able to increase that access beyond what was originally permitted.
Affected SearchStax Deployments
This vulnerability may affect SearchStax Managed Search deployments running on Linux versions released after 2017.
SearchStax is reviewing affected Managed Search environments and will apply the required operating system patches through the standard vulnerability management process.
Mitigation Plan
SearchStax operations teams will patch affected Managed Search deployments based on priority.
Customers with the Security Pack add-on will receive the patch first. After that, patching will proceed by deployment tier in the following order:
- Platinum Plus
- Platinum
- Gold
- Silver
This sequencing allows SearchStax to apply mitigation work in a controlled order while prioritizing customers with Security Pack coverage and higher deployment tiers.
Customer Action Required
No customer action is required.
SearchStax will handle the patching process for affected Managed Search deployments. Customers do not need to open a support ticket, schedule maintenance or make configuration changes for this mitigation.
Expected Service Impact
There is no expected service downtime for this operating system patch.
SearchStax operations teams will apply the mitigation in a way that is intended to avoid customer-facing disruption. If any deployment-specific issue requires customer communication, SearchStax will follow the appropriate support and notification process.
Ongoing Monitoring
SearchStax will continue to monitor CVE-2026-31431 and any related vendor guidance.
This blog post will be updated if new information becomes available, including changes to severity, scope, mitigation steps, or expected service impact.

Get Our Newsletter
The Stack is delivered bi-monthly with industry trends, insights, products and more
Product manager who focuses on search infrastructure management and helping teams build faster with greater focus and confidence